Update 20151216: This quick post got far more attention than expected. I regret not mentioning that the leakage can easily be prevented via a setting. In practice the problem remains, users in general will have no idea about this being a relevant setting to change and will stay with the default. The best discussion on this can be found in the hacker news thread.
According to the Telegram CEO Pavel Durov, earlier this year the Telegram app was delivering 2 billion messages daily and had 62 million monthly active users. Possibly some of that size can be attributed to Telegram's focus on security and privacy. The Telegram FAQ focuses quite a bit on that and for instance states:
After having read that I was surprised to see the amount of metadata received from my contacts. Most of the metadata is not directly visible in the web and mobile clients, but using a third party client such as vysheng's CLI client any received metadata is displayed:
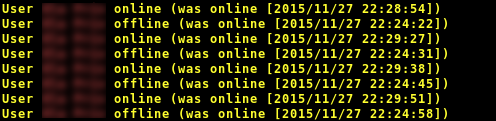
The Telegram android app sends a notification to all contacts when it becomes or stops being the "foreground" app on the device. Using that information alone it's at times easy to make guesses about who's talking to who if you have several contacts in common with a "victim". An "attacker" will sometimes see the victim and another contact taking turns going active/inactive as they pass messages back and forth.
The metadata may be a considerable problem in itself but what makes it worse is that Telegram does not require contacts to mutually agree that they should be connected! As long as an attacker know the phone number of the victim and add it to the android contacts the victim will show up as a Telegram contact and the attacker will automatically subscribe to the victim's metadata. As a bonus the victim will not be notified in any way and the attacker will not show up among the victim's Telegram contacts.
The attacker then takes guesses at what Telegram contacts the victim may have. Adding them as android contacts makes them automatic Telegram contacts and the metadata analysis can begin. Using the metadata the attacker may have a good chance of figuring out who the victim is communicating with and when. That's quite problematic for an app focusing on protecting your conversations from snooping third parties ...
See you on Signal!